Tactic 19. False Peering Outage
This tactic made this playbook famous (in the very narrow micro niche segment of Internet peering operations people).
With this tactic, both the initiator ISP A and the target ISP B are attached to an IXP Public Peering fabric such as an ethernet LAN (Figure 11-34). The target ISP NOC is urgently contacted to “repair” a down peering interconnection. This call is placed in the middle of the night, during a maintenance window when the NOC is manned with a junior on-call engineer. The junior engineer is manipulated into editing the router configuration and establishing peering where peering was never intended to be established.
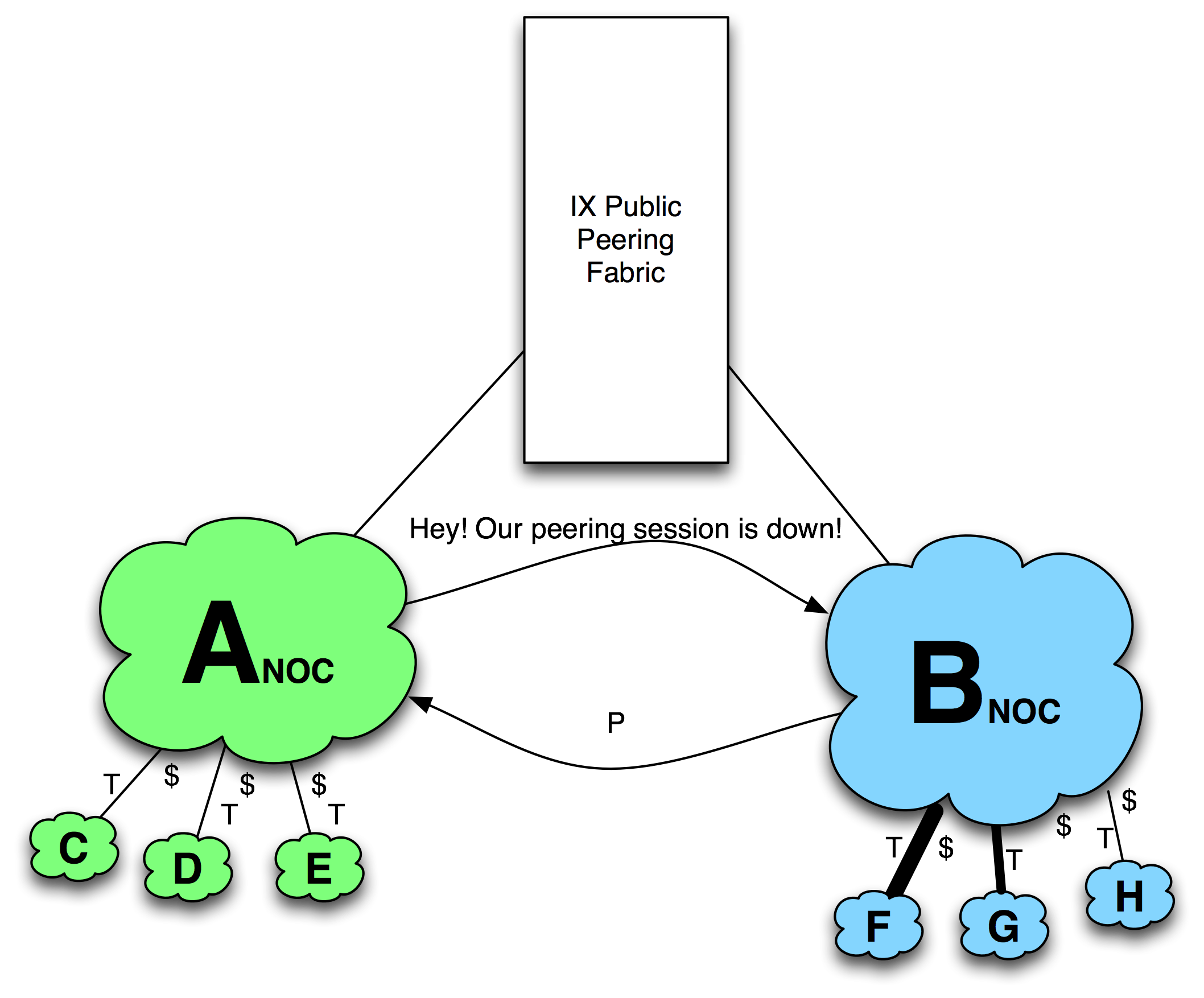
Figure 11-34. The Fake NOC Outage.
The script goes something like this. A Midnight Shift Operator at NOC Acalls NOC B...
NOC A: Hi – our peering session with you is down at IXP North. I am calling to get a status update.
NOC B: Hello, ISP B NOC.
NOC B: I’m not seeing any alerts.
NOC A: I’m telling you it is down. Again. I know you do config runs at this time.
NOC B: Yes we are doing a config run, but I don’t see a peering session configured with you.
NOC A: Well I don’t know what you guys have done, but this is the third time this has happened this year. Don’t make me call Hans-Werner Braun. He will chew you guys out. Again.
NOC B: Umm. I did see something weird and I did hack the config for this bizarre script. I bet it was that last edit that trashed it. Give me a few minutes to fix the config and push it out and I will figure out how to make sure it doesn’t happen again.
When told about this scenario, the most common response from peering coordinators was, “I wonder what our NOC would do?” The VP of Engineering for a large European ISP shared with us that its NOC refers to this tactic by number, as in “Hey, we had another 19 last night.”

